How much data are the most popular apps on Android and iOS leaking to third parties (i.e. people who have nothing to do with the app you’re using). A LOT!
Tag: Security
CFSSL FTW
After reading how CloudFlare handles their PKI and that LetsEncrypt will use it I wanted to give CFSSL a shot.
Reading the project’s documentation doesn’t really help in building your own CA, but searching the Internet I found Fernando Barillas’ blog explaining how to create your own root certificate and how to create intermediate certificates from this.
I took it a step further I wrote a script generating new certificates for several services with different intermediates and possibly different configurations (e.g. depending on your distro and services certain cyphers (e.g. using ECC) may not be supported).
I also streamlined generating service specific key, cert and chain files. 😀
Have a look at the full Gist or just the most interesting part:
You’ll still have to deploy them yourself.
Update 2016-10-04:
Fixed some issues with this Gist.
- Fixed a bug where intermediate CA certificates weren’t marked as CAs any more
- Updated the example CSRs and the script so it can now be run without errors
Update 2017-10-08:
- Cleaned up `renew-certs.sh` by extracting functions for generating root CA, intermediate CA and service keys.
NSA’s MITM attack on Cryptome
The moment you find out the NSA is performing MITM attacks on your website’s visitors from a leaked slide deck:
But here is the thing — and this is crucial — the address for Cryptome is listed to be the location of a fiber optic cable junction in Sterling, VA (next to an Amusement Machine company)… which is quite some distance away from your location in NYC, and a considerable distance from your ISP who hosts your file, and it is located away from any signal switching systems use in the area, but it is virtually next door to fiber that goes to a large NSA listening post nearby.
The reason it is notable, is that someone at or near the location in Sterling, VA is performing a MITM attack on Cryptome visitors, and this image out of the slidedeck with the two GPS coordinates is the U.S. Government performing a MITM attack against Cryptome and sharing the collected intelligence with the Brits, or the U.S. Government giving the British government backdoor access into the U.S. (illegal) collection systems.
Encrypt All Your Devices
Ars Technica has compiled a guide for how to encrypt laptops and phones. There are brief descriptions for all the relevant systems.
New RC Cars
What’s so new about RC cars? Oh … they’re the real, “off-the-shelve” ones, those where people ride in … and they can be hijacked by anybody with the same cellular provider … over the Internet, no direct access required … o.O … WIRED has a piece.
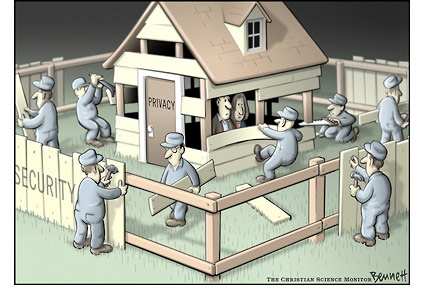
Security Fence
No, You Go First
Bruce Schneier talks about how security companies sat on knowledge and research data about military-grade Regin malware for at least six years. They only decided to share their knowledge because the Intercept was about to publish an article about it. Their arguments for why they withheld their knowledge until now range from “our customers asked us not to disclose what had been found in their networks” to “we didn’t want to interfere with NSA/GHCQ operations”. :/ It’s safe to say that they sit on a bunch more.
Privacy Consequences of the SPE Hack
Bruce Schneier in his comments on the recent Sony Hack cites a Gizmondo article that sums it up very well why privacy is important to everyone even for mundane everyday stuff we do on the internet:
These are people who did nothing wrong. They didn’t click on phishing links, or use dumb passwords (or even if they did, they didn’t cause this). They just showed up. They sent the same banal workplace emails you send every day, some personal, some not, some thoughtful, some dumb. Even if they didn’t have the expectation of full privacy, at most they may have assumed that an IT creeper might flip through their inbox, or that it was being crunched in an NSA server somewhere. For better or worse, we’ve become inured to small, anonymous violations. What happened to Sony Pictures employees, though, is public. And it is total.
And in Bruce’s words:
These people didn’t have anything to hide. They aren’t public figures. Their details aren’t going to be news anywhere in the world. But their privacy has been violated, and there are literally thousands of personal tragedies unfolding right now as these people deal with their friends and relatives who have searched and reads this stuff.
They Don’t Care About Your “Online” Privacy
Messenger apps show your friends’ online status. Anytime you open the app, they’ll notify the service that you’re “online” at the moment. Now everybody else can see it in their contact lists.
And with everybody I mean anybody! If you have a phone number you can check that person’s online status as often as you want from wherever you want (no need to be friends or anything).
So did a group of researchers at the Friedrich-Alexander-Universität Erlangen-Nürnberg. They used this “feature” to “find out how frequently and how long users spent with their popular messenger” on a random sample of 1000 people in different countries for over eight months.
Looking through the project’s website should make it clear how little the creators of those apps care …
Moreover, we were able to run our monitoring solution against the WhatsApp services from July 2013 to April 2014 without any interruption. Although we monitored personal information of thousands of users for several months — and thus strongly deviated from normal user behaviour — our monitoring efforts were not inhibited in any way.
… and that they don’t want you to be able to care.
Unfortunately, affected messenger services (like WhatsApp, Telegram, etc.) currently provide no option for disabling access to a user’s “online” status. Even WhatsApp’s newly introduced privacy controls fail to prevent online status tracking, as users still cannot opt-out of disclosing their availability to anonymous parties.
Choosing Comfort Over Privacy
It looks like Apple “needs” to upload even your unsaved documents to its servers to make the newly introduced Continuity “feature” work.
Also it seems Apple silently uploads names and email addresses of all the people you correspond with–no, not only the ones in your address book–just to have a “consistent” experience when displaying recent addresses.
It scares me how little their customer’s privacy must be worth when they choose (these are not accidental data “leaks”) to silently violate them in order to provide comfort features.
Update 2014-10-30:
It seems there is at least a hidden configuration option to turn this behavior off:
defaults write NSGlobalDomain NSDocumentSaveNewDocumentsToCloud -bool false